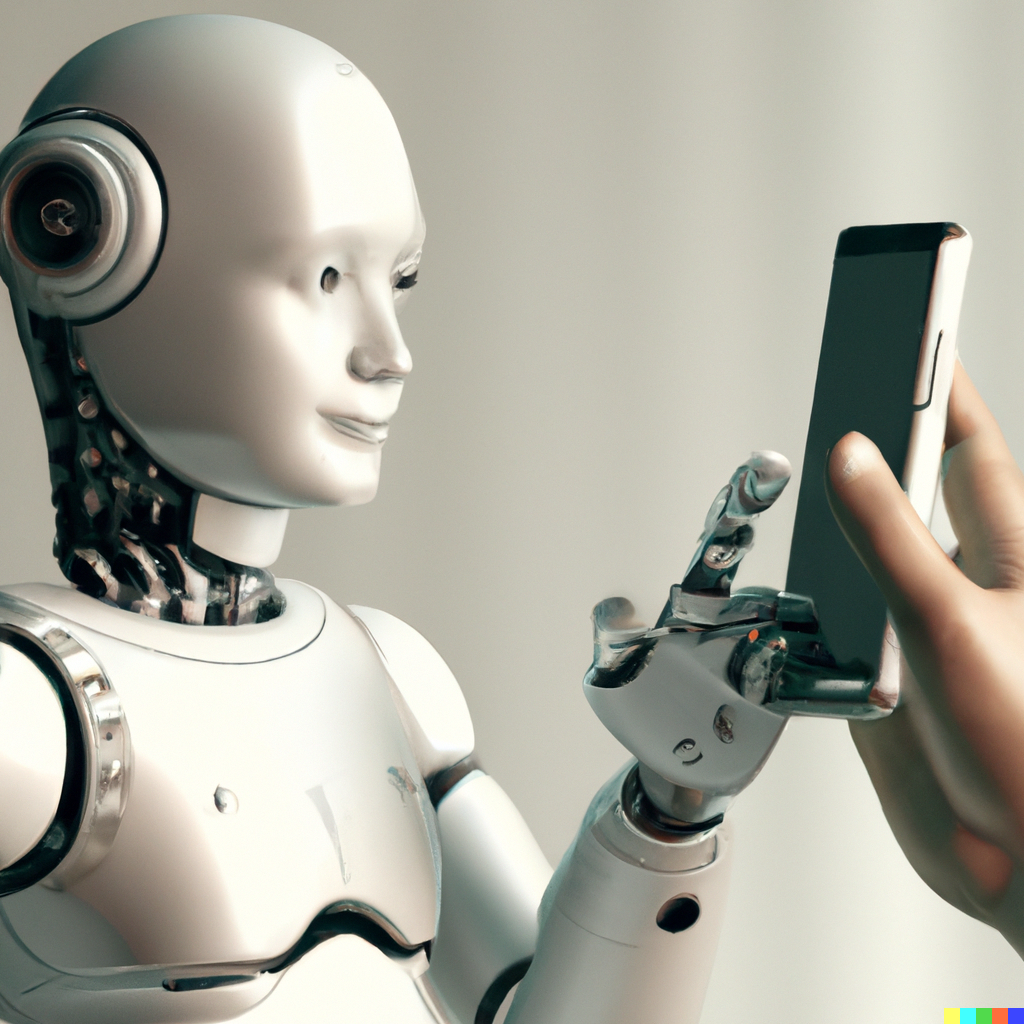
The world can’t stop talking about ChatGPT. It is mighty impressive, but can it only be used for research or writing articles? I used GPT-3 to implement features in my app Values Finder that were previously beyond reach. So now I can say from personal experience: it opens up completely new possibilities.